The cryptocurrency industry likes to present itself as the future of finance, powered by advanced cryptography, decentralized systems, and next-generation technology. Yet behind the scenes, much of the digital asset economy still depends on traditional operating systems that were built decades before Bitcoin even existed.
- What Exactly Is “Copy Fail”?
- Why Public Exploit Code Creates a Bigger Cybersecurity Problem
- Why This Linux Kernel Bug Matters So Much for Crypto Exchange Security
- How the Exploit Works in Real-World Attacks
- Why Security Teams Fear Ransomware and Validator Disruptions
- Why Artificial Intelligence Could Accelerate Future Threats
- What This Means for Everyday Crypto Users
- How Crypto Organizations and Users Can Stay Protected
- Conclusion
- Glossary
- FAQs About Linux Kernel Bug
That hidden dependency is now creating fresh concern after cybersecurity researchers uncovered a dangerous Linux kernel bug capable of threatening exchanges, validators, cloud servers, and crypto wallet infrastructure worldwide.
The vulnerability, known as “Copy Fail,” has reportedly existed inside Linux systems since 2017. Security experts warn that the Linux kernel bug may allow attackers with limited system access to escalate privileges and gain full administrator control over vulnerable machines. Although the flaw does not directly attack blockchain protocols themselves, it creates risks for the infrastructure supporting the crypto industry every day.
That distinction matters because crypto exchange security depends heavily on Linux-based systems. Exchanges, custodial services, validator nodes, hot wallet servers, cloud trading engines, and staking platforms all rely on Linux environments to process billions of dollars in digital asset activity around the clock.
A successful exploit could expose sensitive credentials, interrupt trading systems, or compromise operational infrastructure supporting the broader crypto ecosystem.
Government cybersecurity agencies have already classified the vulnerability as a high-priority threat. At the same time, researchers publicly released proof-of-concept exploit code, raising fears that attackers could rapidly scale exploitation attempts across unpatched systems.
What Exactly Is “Copy Fail”?
The Linux kernel bug belongs to a category of cybersecurity threats called privilege escalation vulnerabilities. In simple terms, the flaw allows someone with ordinary user-level access to gain complete root control over a Linux machine.
The vulnerability reportedly stems from how Linux manages its page cache, a temporary memory storage system designed to speed up file access and improve operating efficiency. Normally, the page cache helps Linux quickly retrieve frequently used files without repeatedly accessing slower storage drives. However, researchers discovered that attackers could manipulate this process and trick the operating system into granting elevated privileges.
Did you know? Linux dates back to 1991, while Bitcoin’s white paper arrived in 2008. Much of today’s crypto infrastructure still runs on operating system foundations older than blockchain technology itself.
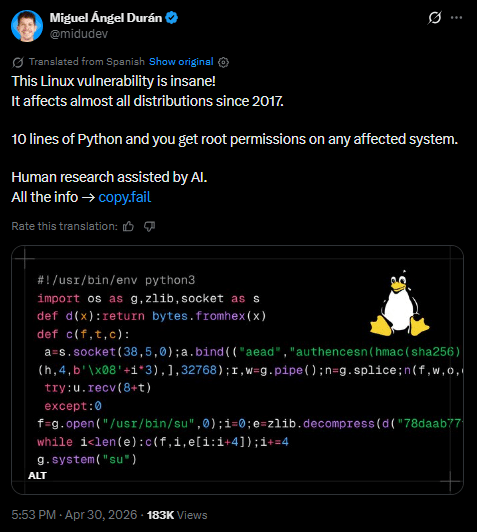
What makes this Linux kernel bug especially alarming is how easy it appears to exploit. According to security researcher Miguel Angel Duran, attackers may need only around 10 lines of Python code to gain root access on vulnerable Linux machines. Researchers say the exploit can reliably work across multiple Linux environments, dramatically increasing operational risk for crypto infrastructure teams.
That simplicity dramatically changes the operational threat landscape.
Why Public Exploit Code Creates a Bigger Cybersecurity Problem
Cybersecurity teams often become far more concerned once proof-of-concept exploit code appears publicly online. That concern is not simply theoretical.
Once attackers gain access to working exploit scripts, they can quickly integrate them into automated exploit kits, malware frameworks, and botnet scanning tools. Low-skill hackers no longer need deep Linux expertise when copy-paste exploit packages become widely available on underground forums.
The Linux kernel bug therefore creates operational risk far beyond advanced hacking groups. Automated bots can continuously scan the internet searching for vulnerable Linux servers tied to exchanges, validator nodes, cloud virtual machines, and wallet infrastructure.
Attackers may also combine phishing attacks with automated privilege escalation tools. A compromised employee account with basic access could suddenly become a gateway into much larger infrastructure environments once the Linux kernel bug enters the attack chain.
This rapid scaling effect explains why crypto exchange security teams are reacting aggressively. In modern cybersecurity, vulnerabilities become much more dangerous once exploitation becomes automated and repeatable at internet scale.
Why This Linux Kernel Bug Matters So Much for Crypto Exchange Security
Linux powers enormous portions of the cryptocurrency ecosystem. Exchanges use Linux-based cloud systems to process trades, manage APIs, support liquidity infrastructure, and operate wallet management services.
Crypto exchange security also depends heavily on:
- validator nodes,
- staking systems,
- custodial infrastructure,
- blockchain explorers,
- mining operations,
- and hot wallet servers.
Hot wallets deserve special attention because they remain connected to the internet for fast transaction processing. Many exchanges rely on Linux-based hot wallet infrastructure to support withdrawals, deposits, and trading operations in real time. If attackers gain root access to those environments, they may potentially access wallet credentials, authentication systems, or sensitive operational data.
Cold wallet systems remain safer because they stay offline most of the time. However, custodial infrastructure often connects cold storage management tools to broader operational networks at certain stages, creating additional security considerations.
Did you know? Many large crypto exchanges use Kubernetes orchestration systems to manage clusters of Linux servers supporting blockchain nodes, trading engines, and wallet infrastructure simultaneously.
This operational complexity means crypto exchange security increasingly depends on securing ordinary cloud infrastructure as much as protecting blockchain protocols themselves.
How the Exploit Works in Real-World Attacks
The Linux kernel bug does not operate as a direct remote exploit launched instantly from the internet. Attackers first need some type of foothold inside the target environment.
That initial access often comes through:
- phishing campaigns,
- leaked credentials,
- infected software,
- compromised cloud accounts,
- vulnerable web applications,
- or weak administrator passwords.
Some observers mistakenly downplay the threat because attackers require initial access first. In reality, most major cyberattacks unfold in multiple stages rather than a single dramatic breach.
A typical attack chain may look like this:
- attackers steal low-level credentials,
- they access a Linux environment,
- they exploit the Linux kernel bug,
- they obtain root privileges,
- then they expand deeper into the network.
Did you know? Root access functions much like possessing the master key to an entire skyscraper. Once attackers gain it, they may control nearly every system running inside the building.
That progression explains why crypto exchange security remains highly vulnerable to privilege escalation flaws. Many past exchange breaches started with something as simple as a phishing email or compromised administrator credentials.

Why Security Teams Fear Ransomware and Validator Disruptions
The Linux kernel bug also creates concern because ransomware groups increasingly target cloud infrastructure rather than ordinary personal devices.
In several previous cyber incidents across the financial and technology sectors, attackers compromised internal Linux environments before deploying ransomware capable of shutting down operational systems. Similar tactics inside crypto infrastructure could interrupt exchange services, freeze withdrawals, or disable validator participation.
Validator downtime creates another serious concern. Blockchain validators help confirm transactions and maintain network stability. If attackers compromise validator nodes supporting staking platforms or blockchain infrastructure providers, service interruptions could ripple across broader ecosystems.
Crypto exchange security teams also worry about attackers disabling monitoring systems after obtaining root privileges. Once visibility disappears, malicious activity may continue unnoticed for extended periods.
Cloud virtual machines, Kubernetes clusters, and container orchestration systems introduce additional complexity. Poorly configured container permissions may allow attackers to move laterally across interconnected infrastructure after exploiting a Linux kernel bug.
Why Artificial Intelligence Could Accelerate Future Threats
The emergence of advanced AI systems is reshaping cybersecurity rapidly. Researchers increasingly believe AI tools can identify exploitable vulnerabilities far faster than traditional manual auditing methods.
Modern AI systems may assist attackers through:
- automated code auditing,
- AI-assisted exploit generation,
- vulnerability discovery acceleration,
- phishing automation,
- and autonomous attack tooling.
That evolution matters because blockchain infrastructure often combines multiple open-source technologies together. Exchanges may simultaneously operate Linux servers, cloud APIs, validator software, databases, orchestration systems, and wallet infrastructure across enormous distributed environments.
As AI systems improve at analyzing software code, attackers may discover and weaponize future Linux kernel bug vulnerabilities much faster than before.
At the same time, defenders can also use AI-driven security tools to identify weaknesses earlier and strengthen crypto exchange security before attacks spread.
What This Means for Everyday Crypto Users
For most ordinary crypto holders, the Linux kernel bug does not create direct personal exposure. However, indirect effects could still impact millions of users if exchanges or custodial providers suffer infrastructure compromises.
Possible consequences include:
- frozen withdrawals,
- exchange downtime,
- wallet disruptions,
- data exposure,
- validator outages,
- or delayed transaction processing.
Self-custody users operating personal validators or Linux-based blockchain nodes face higher operational risk and should prioritize system updates immediately.
Crypto exchange security also depends heavily on user behavior. Many large infrastructure breaches begin with simple phishing attacks targeting employees, contractors, or administrators rather than advanced blockchain exploits.
How Crypto Organizations and Users Can Stay Protected
The positive news is that most risks tied to the Linux kernel bug remain manageable when organizations act quickly.
Crypto firms should deploy kernel patches immediately and audit cloud virtual machines regularly. Security teams should also strengthen SSH authentication, monitor unusual privilege escalation attempts, reduce administrator access, and isolate validator infrastructure carefully.
Container permissions and Kubernetes orchestration settings deserve close review because poorly segmented environments may allow attackers to spread across systems after gaining root access.
Meanwhile, individual users should:
- enable multi-factor authentication,
- avoid unofficial crypto tools,
- keep operating systems updated,
- use hardware wallets for large holdings,
- and separate high-value wallet activity from everyday browsing environments.
Conclusion
The Linux kernel bug known as Copy Fail exposes an uncomfortable truth about modern cryptocurrency infrastructure. Blockchain networks may rely on advanced cryptography and decentralized consensus systems, but the servers supporting those ecosystems still depend heavily on traditional operating systems vulnerable to ordinary cyberattacks.
That reality means attackers no longer need to break blockchain encryption directly to create massive disruption. Sometimes compromising the infrastructure beneath the blockchain becomes enough.
As AI-powered cybersecurity threats evolve and crypto infrastructure grows more interconnected, crypto exchange security may increasingly depend on disciplined operational defense rather than blockchain technology alone.
The next major crypto security crisis may not begin on-chain. It may begin deep inside the operating systems quietly powering the digital asset economy every single day.
Glossary
Linux Kernel Bug: A flaw inside the core Linux operating system code.
Privilege Escalation: A method attackers use to gain higher system permissions.
Root Access: Full administrator-level control over a Linux system.
Page Cache: Temporary memory storage Linux uses for faster file access.
Hot Wallet: An internet-connected crypto wallet used for fast transactions.
Cold Wallet: An offline wallet designed for safer long-term storage.
Validator Node: A blockchain server responsible for confirming transactions.
Kubernetes: A cloud orchestration platform used to manage containerized systems.
FAQs About Linux Kernel Bug
Why is the Linux kernel bug dangerous for crypto exchanges?
Because exchanges rely heavily on Linux-based cloud infrastructure, wallet servers, validators, and trading systems that may become vulnerable to privilege escalation attacks.
Does the vulnerability directly attack blockchain networks?
No. The Linux kernel bug targets operating systems rather than blockchain protocols themselves.
Why does public exploit code matter?
Public exploit scripts allow attackers to automate attacks using botnets, exploit kits, and low-skill copy-paste hacking techniques.
Can AI make vulnerabilities like this more dangerous?
Yes. AI systems may accelerate exploit generation, vulnerability discovery, automated phishing, and attack scaling.