Cryptocurrencies are secured by private keys held in wallets but not all wallets are created equal. According to available data; hackers stole more than $2.2 billion from crypto users in 2024; mostly due to compromised keys. This reality makes the choice between hot wallets vs cold wallets crucial.
- What Is a Crypto Wallet?
- How Hot Wallets Work
- How Cold Wallets Work
- Hot Wallets vs Cold Wallets: A Quick Comparison
- Security Risks and Threats for Hot Wallets vs Cold Wallets
- Cost, Setup, and Usability for Hot Wallets vs Cold Wallets
- Expert Analysis and Institutional Trends on Hot Wallets vs Cold Wallets
- Conclusion
- Glossary
- Frequently Asked Questions About Hot wallets vs Cold Wallets
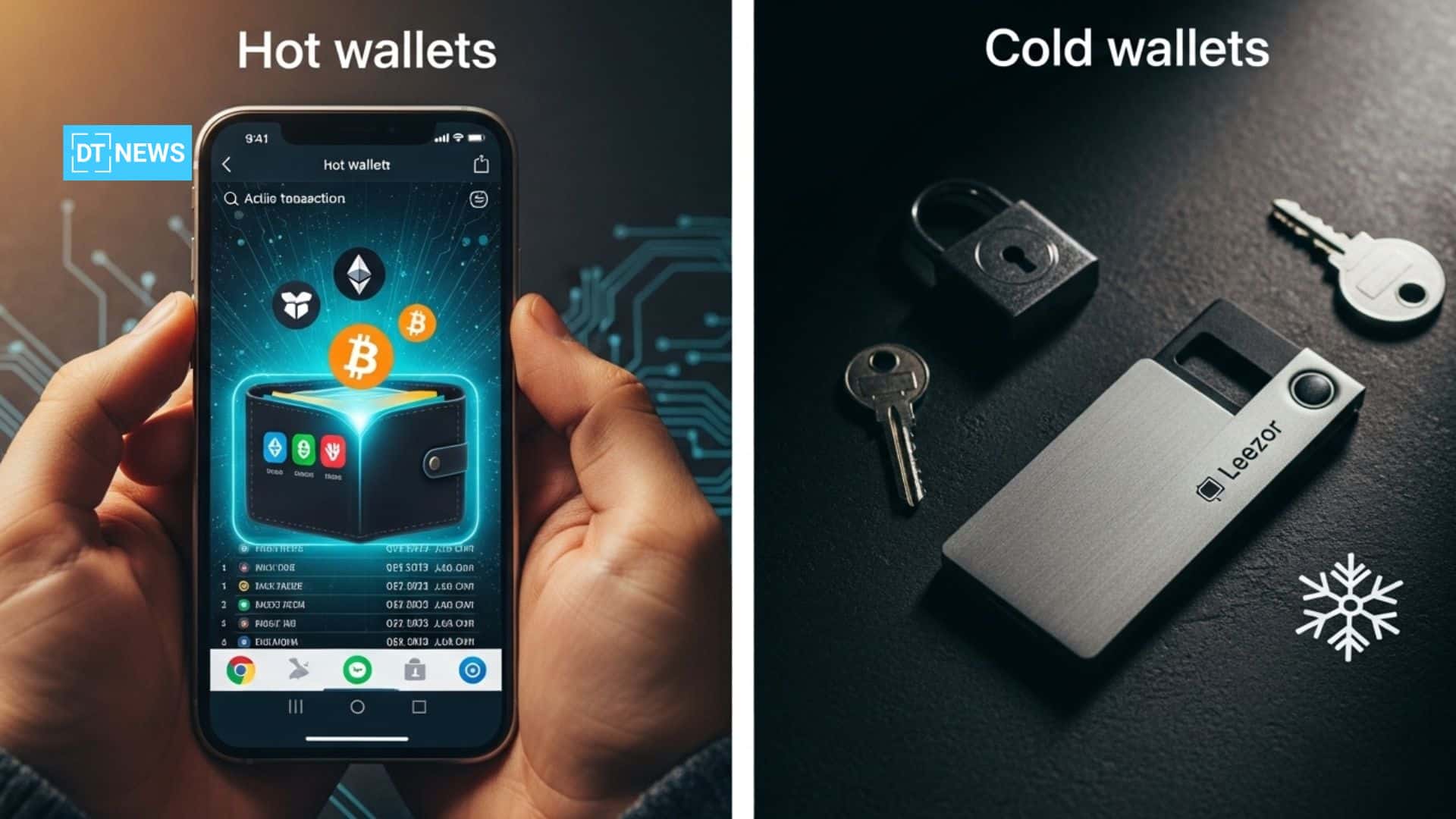
A crypto wallet holds the private keys that unlock your digital assets. These wallets come in two main types: Hot wallets that remain online for accessibility to trade; and cold wallets that hold keys offline for maximum security.
A hot wallet lets users quickly send and receive crypto but exposes users to cyber threats. Cold wallets keep the keys offline thus lowering the risk of hacking but at a huge convenience cost.
What Is a Crypto Wallet?
A cryptocurrency wallet is not a bank account nor storage of coins, it is a tool that carries cryptographic keys. This involves two keys; one private key (a secret passcode that allows you to spend your crypto) and the other public key/address (which you share with others for them to be able to send you crypto).
To put it another way, users’ coins are never actually in the wallet; they always live on the blockchain and the only thing the wallet holds is the keys to access them.
Wallets can be broadly categorized as hot wallets vs cold wallets based on their internet connection.
A hot wallet is any wallet connected to the internet; via a smartphone app (Coinbase Wallet, Trust Wallet), desktop program or through an account on an exchange. A cold wallet is one that is kept offline; usually a hardware device (like Ledger or Trezor), a USB drive, or even just a paper/metal backup of your seed phrase.
Cold wallets are usually immune from online hacking attempts due to being offline. However, cold wallets can be lost, stolen or damaged, so users must keep their seed phrase very secure.
Wallets also differ by custody. Users can hold self-custody (with you keeping the private keys under your control) or custodial service (holding them by a third party).
Both hot wallets vs cold wallets options exist in self-custody or custodial forms. An example of a self-custody hot wallet is a hardware wallet, while many exchanges provide custodial hot wallets. But in either case, if you lose the keys and there is no backup (or if it has not been properly documented), then the crypto cannot be recovered.
How Hot Wallets Work
Hot wallets focus on providing a user-friendly experience. As they are online, these enable swift trades and quick access to funds making them great for active traders or day-to-day use. Hot wallets include:
Desktop wallets: These are software programs that you have installed on your PC (Electrum, Exodus). They allow a compromise between security and convenience; but if malware hits the computer, they may be compromised.
Mobile wallets: Apps on your smartphone (Trust Wallet, Coinbase Wallet, etc.). These are good for accessing your cryptocurrency quickly, although if you lose or get your phone hacked; it may jeopardize your funds.
Web wallets / Browser Extension: Online wallets like MetaMask or web interface of exchanges. These are accessible from any device, but the security of the website and the safety of the browser needs to be trusted.
One big advantage of hot wallets is their accessibility because transactions can be signed and broadcast immediately. Most hot wallets support multiple coins and integrate easily to decentralized apps. This internet capability, however, is also the main weakness of hot wallets.
They are “internet-connected and transaction ready,” making them vulnerable to cyber-assaults. Hackers use phishing, malware or compromised apps to take keys or manipulate users by tricking them into signing malicious transactions.
If you use a hot wallet on an exchange, you are effectively trusting that exchange with your private keys; if the company servicing the hot wallet is hacked or goes bankrupt, they could disappear overnight (and many exchanges have) with any funds inside it.
This means that even non-custodial hot wallets can leak if your device is compromised. As a result, a lot of hot wallets provide security features such as password protection, two-factor authentication, and integration with hardware keys to minimize some risks.
How Cold Wallets Work
Cold wallets store private keys offline; this option reduces online threat attack significantly. The most common type is a hardware wallet. This is a physically secured device (like a USB key or special card) holding keys on a tamper-resistant chip.
When users wish to perform a transaction; they connect the device to a computer or phone (typically via USB or Bluetooth); check the details of the transaction on its screen and approve it manually. In this way; the private key never leaves the device and will not touch the internet.
Cold storage methods also include air-gapped wallets, these are computers that are not connected networked; users send transactions using QR codes or drives) and even paper/steel-based backups, where users write or engrave their seed phrases on a physical medium.
These methods ensure no digital copy of the key is accessible online. According to sources, cold wallets are offline devices and are usually deemed more secure for long-term crypto storage.
However, cold wallets are less convenient. They are not suitable for a fast trade since every withdrawal needs to be done in several steps (connecting the device, approving on the screen, etc.). Hot wallets are usually free, while hardware wallets typically cost between $50 and $200 each.
Conversely though, cold devices exist physically and they can be lost, damaged, or stolen (and forgetting your seed phrase back up means losing the crypto).
Hot Wallets vs Cold Wallets: A Quick Comparison
| Feature / Factor | Hot Wallets | Cold Wallets |
| Connectivity | Always online (internet-connected) | Offline by default; connects only to transact |
| Use Case | Daily use, frequent trading, small balances | Long-term storage, large balances, inheritance |
| Security | More exposed to online hacks and phishing | Protected from online threats; vulnerabilities are physical (loss, theft) |
| Convenience | Very convenient & fast | Requires extra steps (plug in device, review, approve) |
| Cost | Usually free (software, exchange accounts) | Hardware devices cost ~$50–$200; paper/backups are cheap |
| Recovery | Recoverable via seed phrase if backed up properly | Also recoverable via seed phrase; risk if phrase lost or damaged |
| Examples | Coinbase Wallet, MetaMask, Trust Wallet | Ledger Nano, Trezor, paper wallets |
Hot wallets are more convenient and faster than cold wallets, but from a security perspective, cold wallets win. As advised by the SEC, consider your “convenience and security” needs in choosing which form of crypto wallet may suit you best.
Security Risks and Threats for Hot Wallets vs Cold Wallets
The main difference between hot wallets vs cold wallets comes down to security. Hot wallets have majorly been the target of most crypto thefts. Online wallets are often susceptible to threats like malware, phishing sites, and exchange hacks.
In recent years, reports have covered that giant exchange hacks and phishing scams have accounted for billions in losses. These online risks are almost completely mitigated by cold wallets.
Typical hacks cannot access the keys because they are not connected. But cold wallets are not at all unhackable. Physical attacks on devices are possible: researchers have already demonstrated side-channel attacks (observing power usage or electromagnetic emissions) on certain hardware wallets.
Also, when you purchase a hardware wallet through unofficial vendors; thieves could pre-program it with a backdoor.
Even simply the theft or damage of a hardware device can cost you all your crypto if you don’t have a safe backup of the seed phrase. (Note: even if a bad actor steals your hardware wallet, they still need the seed phrase to move funds.)
Another risk is imperfect user behavior. An example of this is that heads sometimes write seed phrases on sticky notes (which can be lost or photographed), or fall victim to fake wallet apps, etc.
Cybersecurity professionals and the SEC emphasize a few rules: don’t share your seed phrase, make sure any device used is fortified (set passwords & PIN) and always double check transaction details before finalizing them.
Recent research has shown that cold wallet solutions now include screens so you can verify the exact amount and destination on the device itself; preventing hidden malware from altering transactions.
To wrap it all up; hot wallets are easy-to-use but present high cyber risk; cold wallets are free from those cyber risks but require discipline and carefulness to maintain physical security.

Cost, Setup, and Usability for Hot Wallets vs Cold Wallets
Hot wallets are mostly free and can often be set up quickly. Most exchanges or mobile wallets can be configured within minutes using an email or seed phrase. On the other hand, for cold wallets; you have to buy hardware ($50-200) and learn how to use it compared to hot wallets. You have to carefully install all necessary software (e.g, Ledger Live) and create seed backups safely.
However; for most users, the added cost of cold storage is worth it for peace of mind. Industry reports note hardware wallet revenues grew sharply, driven by demand for secure storage. According to Mordor Intelligence; the hardware wallet market is expected to grow 25% annually and reach $0.72billion in 2026.
Today’s wallet technology also blurs some lines. For example, some smartphone wallets use Secure Enclave or Trusted Execution hardware (like Apple’s Secure Element) to keep keys safer, while still calling them “hot” because they connect to networks.
There are also smart contract wallets (like Argent or Gnosis Safe) that sit on blockchains and add recovery options or multisig.
These new classes often combine elements of hot wallets vs cold wallets together: they use on-chain code (which is always online) but may require hardware signers or multiple approvals (the offline parts) for security.
Expert Analysis and Institutional Trends on Hot Wallets vs Cold Wallets
Security experts and institutions stress a need to use both hot wallets and cold wallets together. Institutional guides often advise to keep 80-90%+ of all assets in cold storage and only a modest active balance in hot wallets to meet daily needs.
This two-tier framework provides a balance of security and flexibility.
Regulators from around the world are also coming into the space. New banking charters in the U.S. and FINRA/OCC guidance promote best custody practices. In Europe; MiCA (effective Dec 2024) imposes stringent custody rules on crypto service providers, including segregation of client assets and mandatory insurance.
As a result, major custodians and exchanges now routinely use hardware security modules (HSMs); multi-signature setups, and geographic cold-storage vaults to protect assets.
Notably, after recent breaches; many companies brought in third-party auditors to pen-test their systems and certify their cold storage procedures (as recommended by security firms).
Conclusion
Hot wallets vs cold wallets demonstrates an important security vs convenience compromise. Hot wallets give users the fastest access to their crypto but have a high risk of being hacked. Cold wallets protect keys offline, which means they are much less exposed to online assault, however they also require more effort and care.
Most experts; however, suggest a mixed approach of using a hot wallet for day-to-day spending or trading and keeping the rest of your cryptocurrency in a cold wallet.
A user’s personal preference depends on their comfort with tech; the size of their holdings and access speed requirements. Weighing these factors will help you pick the right combination of hot wallets vs cold wallets for your specific needs.
Glossary
Private Key: A secret code that confirms you own the crypto assets and allows users to perform each transaction.
Public Key / Address: A code that is derived from the private key. You share this in order to get funds.
Seed Phrase: A set of words that your wallet creates. The reason to note down this phrase is that it lets you recover your wallet private key if the device gets lost.
Self-Custody: You hold and own your private keys (
Custodial Wallet: A wallet service (e.g. an exchange) keeps your private keys for you.
Multi-Signature Wallet: A wallet that requires multiple signatures (or approvals) from different devices or parties to approve a transaction.
Air-Gapped Wallet: a type of cold wallet setup where your signing device is not connected to the internet at all; and data is transferred only through QR codes or USB.
Frequently Asked Questions About Hot wallets vs Cold Wallets
What is a hot wallet?
A hot wallet refers to any cryptocurrency wallet that is connected to the internet. They provide immediate access to your funds; but they are more vulnerable to online scams.
What is a cold wallet?
A cold wallet is a wallet that stores cryptocurrency offline. They keep your keys safe from online hacks; but you have to take very deliberate steps each time you want to perform a transaction.
Which is safer: hot wallets vs cold wallets?
As offline wallets keep keys offline, they are generally safer from online threats. Hot wallets; while convenient, pose a greater risk for hacks or phishing schemes.
Can I lose my cryptocurrency if I lose my wallet?
If you ever lose access to any wallet (hot or cold) without backup; you will end up losing that crypto. But every wallet that can be trusted has an option to have a seed phrase backup. When you note this seed phrase down (on paper or metal) it allows you to restore your wallet on a different device if the first one is lost.
Should I use both hot and cold wallets?
Experts recommend using both. Store a portion in a hot wallet for transaction / trading purposes while retaining the majority in cold storage.
References
Disclaimer: This article is only for educational purposes and not financial investment advice. Readers should do their own research before taking any actions based on the information provided here.