Zero-knowledge proofs have become a cornerstone technology for privacy-focused blockchain development in 2026, giving developers the ability to verify information without ever revealing sensitive details. As Web3 networks face increasingly strict regulatory requirements alongside the rising threat of AI-driven security attacks, zero-knowledge proofs offer a practical and scalable solution that balances transparency with user confidentiality.
- What Are Zero-Knowledge Proofs and Why Do They Matter?
- How Did Zero-Knowledge Proofs Evolve into Modern Applications?
- How Are Developers Using Zero-Knowledge Proofs Today?
- What Tools and Practices Optimize Zero-Knowledge Proof Development?
- How Does the Zero-Knowledge Proof Workflow Operate?
- What Challenges Remain in Implementing Zero-Knowledge Proofs?
- Conclusion
- Glossary
- Frequently Asked Questions About Zero-Knowledge Proofs 2026
Analysts highlight that the adoption of these advanced cryptographic protocols is expanding quickly across multiple sectors, including decentralized finance platforms, enterprise-level compliance systems, and digital identity verification solutions. Experts further emphasize that zero-knowledge proofs are evolving into essential tools for developers who aim to build secure, privacy-preserving applications that function effectively on both public and private blockchain networks.
What Are Zero-Knowledge Proofs and Why Do They Matter?
Zero-knowledge proofs let a prover convince a verifier that a statement is true without revealing any of the underlying information. This method works based on three main principles: completeness, soundness, and zero-knowledge. These rules make sure that honest proofs are always accepted, dishonest attempts are nearly impossible, and no extra information is revealed during verification.
With zero-knowledge proofs, developers can confirm credentials, account balances, or identity details without sharing the full dataset. In 2026, analysts say these capabilities are crucial for building Web3 applications that prioritize user privacy while complying with strict data-minimization rules.
How Did Zero-Knowledge Proofs Evolve into Modern Applications?
Zero-knowledge proofs were first developed in 1985 as interactive protocols that needed several rounds of communication between a prover and a verifier. Later, the creation of non-interactive versions, such as zk-SNARKs, allowed these proofs to work efficiently in asynchronous blockchain settings.
The real-world use of zero-knowledge proofs grew with Zcash’s shielded transactions and Ethereum’s layer-2 scaling solutions. By 2026, development frameworks for zk-SNARKs, zk-STARKs, PLONK, and Halo2 have reached full maturity, enabling developers to implement secure and efficient proofs across decentralized applications. Experts point out that these frameworks convert decades of cryptography research into practical tools suitable for production-level blockchain systems.
How Are Developers Using Zero-Knowledge Proofs Today?
Zero-knowledge proofs underpin selective disclosure in identity systems, enabling users to prove attributes such as KYC compliance or educational credentials without sharing full documents. ZK-rollups illustrate the scalability impact, bundling thousands of transactions into single proofs and achieving up to 100x throughput on Ethereum while retaining mainnet security.
Enterprise adoption is growing rapidly. Supply chains prove product provenance, healthcare systems verify treatment eligibility, and financial institutions demonstrate regulatory compliance, all through zero-knowledge proofs. Analysts observe that these applications are driving framework maturity and increasing demand for skilled developers.
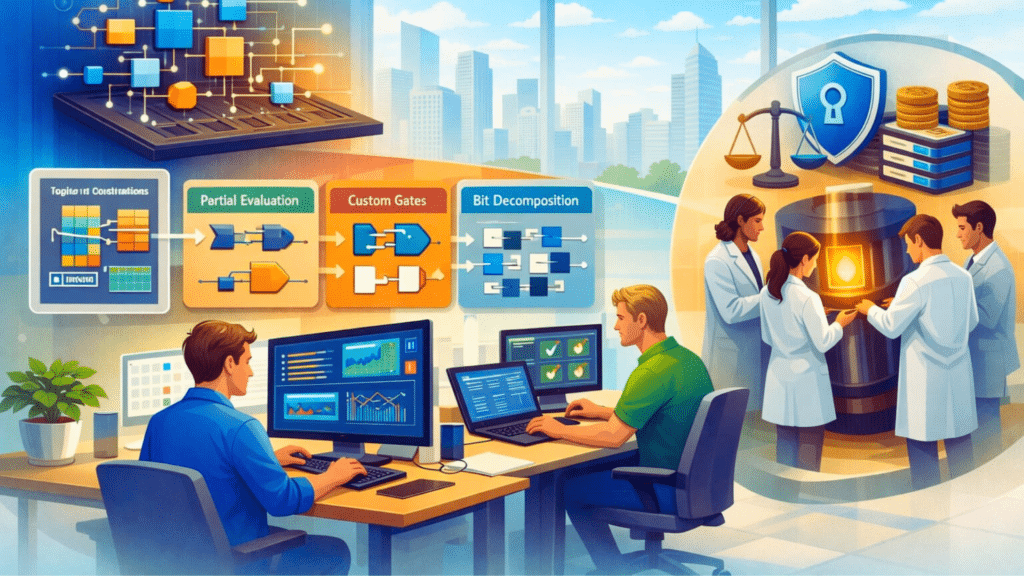
What Tools and Practices Optimize Zero-Knowledge Proof Development?
Developers use frameworks such as Circom, Halo2, and Noir to create circuits and generate zero-knowledge proofs efficiently. Hardware acceleration through multi-GPU setups or FPGA deployments can greatly reduce computation times. Recommended practices include breaking circuits into smaller subcircuits, optimizing lookup operations, and applying static analysis tools to catch underconstrained signals before deployment.
Understanding the underlying mathematics, including finite field arithmetic and elliptic curve pairings, is crucial to maintaining accuracy and security in proofs. Techniques like recursive proof composition and partial evaluation further help lower computation costs and reduce mainnet gas usage, making zero-knowledge proofs more practical for large-scale applications.
Different types of zero-knowledge proofs offer distinct benefits and trade-offs. zk-SNARKs produce small proofs and allow fast verification but require a trusted setup. zk-STARKs remove the need for trusted setups and provide post-quantum security, though their proofs are larger.
Universal frameworks like PLONK and Halo2 allow reusable setups, support flexible circuit designs, and simplify development across multiple projects. The ecosystem around zero-knowledge proofs is strong, with hackathons, protocol grants, and open-source frameworks supporting developer learning and experimentation, although initial setup and the learning curve can present some challenges for newcomers.
How Does the Zero-Knowledge Proof Workflow Operate?
Zero-knowledge proofs follow a clear and organized workflow. Developers first model application logic as an arithmetic circuit, which is then transformed into a Rank-1 Constraint System (R1CS) representing relationships such as A⋅B=C. During setup, proving and verifying keys are generated.
Private inputs are used to create compact proofs, which verifiers can check along with public inputs in just milliseconds. Solidity verifier contracts can be deployed once and then used to validate an unlimited number of proofs, providing a practical and efficient path for integrating zero-knowledge proofs into production applications.
What Challenges Remain in Implementing Zero-Knowledge Proofs?
Circuit optimization continues to be one of the main challenges in implementing zero-knowledge proofs. Large numbers of constraints can significantly slow down proof generation, so developers address this by breaking circuits into smaller modules and improving repetitive operations. Common optimization methods include lookup arguments, partial evaluation, custom gates, and bit decomposition.

Lookup arguments can cut constraints by up to 70%, partial evaluation by 50%, custom gates by 40%, and bit decomposition by 30%, all of which noticeably increase proving speed. Automated testing frameworks help ensure that edge cases and boundary conditions are thoroughly validated before deployment on the mainnet.
Trusted setup ceremonies, while partially resolved through universal protocols such as PLONK, still raise concerns over transparency. Maintaining the right balance between efficiency, security, and developer productivity remains essential for broad adoption in 2026.
Conclusion
Zero-knowledge proofs have firmly established themselves as critical infrastructure for privacy-focused Web3 applications. From confidential DeFi transactions to enterprise compliance and selective disclosure systems, these proofs allow developers to balance transparency with data confidentiality effectively.
In 2026, having expertise in zero-knowledge proofs is not just a technical benefit but a strategic requirement. Developers who successfully implement these protocols will be at the forefront of building applications where users fully control their data while still enabling verifiable operations, helping shape the next generation of decentralized ecosystems.
Glossary
PLONK: Universal ZKP framework with reusable setup for flexible circuits.
Halo2: Advanced ZKP framework for custom, scalable proofs.
Circom: DSL for creating arithmetic circuits used in ZKPs.
Noir: High-level language simplifying ZKP app development and optimization.
Custom Gates: Circuit parts that speed up specific ZKP logic.
Frequently Asked Questions About Zero-Knowledge Proofs 2026
How do ZKPs protect user privacy?
ZKPs allow verification of credentials, balances, or identity attributes without sharing the full data.
What types of ZKPs are commonly used?
The main types include zk-SNARKs, zk-STARKs, PLONK, and Halo2, each with different strengths and trade-offs.
How do developers create ZKPs?
Developers model application logic as arithmetic circuits, compile them into R1CS, generate proofs, and verify them on-chain.
What challenges exist in using ZKPs?
ZKPs can be slow for large circuits, require optimization like custom gates and lookup arguments, and sometimes need trusted setups
What tools help build ZKPs?
Frameworks like Circom, Halo2, Noir, and PLONK help design circuits, generate proofs, and optimize performance.