Decentralized compute has struggled to meet expectations in providing truly trustless cloud infrastructure. While these networks are capable of efficiently discovering idle GPUs and coordinating payments across participants, the element of trust is still centralized, meaning users have to rely on the honesty and accuracy of node operators to ensure computations are correct.
Between 2023 and 2025, investors directed an enormous $2 billion to $3 billion into “decentralized cloud” tokens, reflecting high confidence in the technology, yet no existing network is able to mathematically guarantee that the work performed by nodes is accurate or verifiable. Until robust cryptographic verification methods are put in place, decentralized compute remains mostly suitable for basic rendering jobs and hobbyist workloads, rather than serving complex, enterprise-scale applications that demand full reliability and trustless assurance.
How Does Decentralized Compute Work and Why Is Trust a Concern?
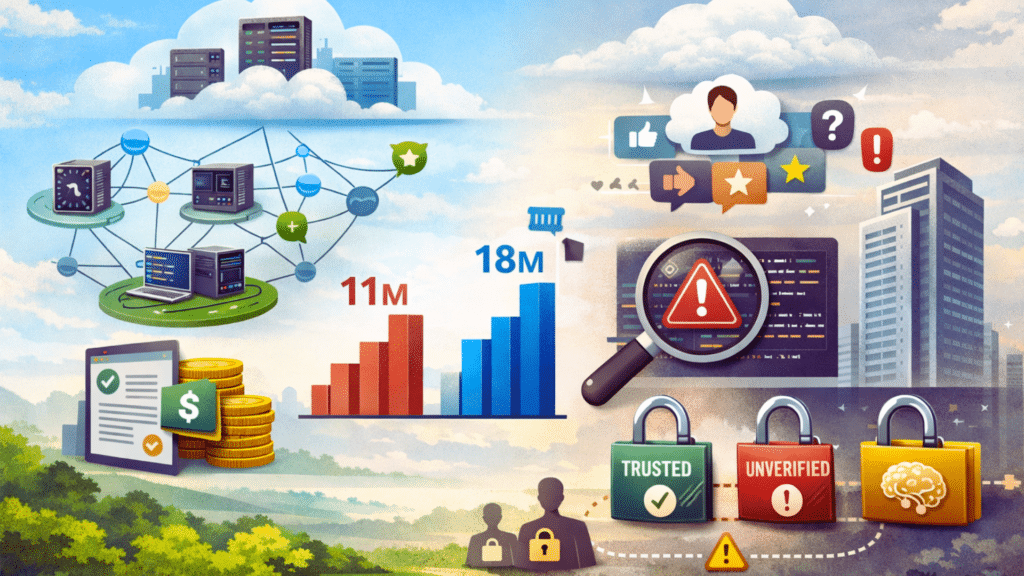
Decentralized compute works by spreading tasks across independent nodes, with the goal of replacing traditional cloud providers. Platforms like Akash and Render can efficiently locate available GPUs and manage payments across their networks. In Q3 2025, Akash generated $11 million in revenue, while Render reached $18 million; however, these amounts are still very small compared to AWS, which reports an annual run rate exceeding $100 billion.
Even though supply and payments are decentralized, the element of trust remains centralized. Nodes return results along with reputation scores, but these scores do not provide mathematical proof of correctness. Vitalik Buterin highlighted this issue at Devcon 2024, stating “If your scaling solution reintroduces trusted parties, you haven’t scaled. You’ve just outsourced.” Without proper verifiable computation, sensitive and high-value workloads continue to be at risk of errors or manipulation.
What Failures Highlight the Limits of Current Networks?
Real-world incidents have shown the weaknesses in current decentralized compute networks. Corrupted Blender renders and Sybil attacks on airdrops prove that relying on social enforcement and reputation alone cannot replace mathematical verification. These issues create significant barriers for adoption in high-value use cases, including AI inference, financial computations, and proprietary workloads.
While these networks do decentralize GPU resources, they do not decentralize trust. Users are forced to accept results without any independent way to verify them, which compromises the promise of truly trustless infrastructure.
What Is the Path Forward for Decentralized Compute?
The path forward depends on verifiable computation. Using cryptographic proofs like zkSNARKs, STARKs, or optimistic fraud proofs can guarantee that every computation is correct. Hardware-accelerated proving systems with FPGAs and ASICs make it possible to verify results at large scale efficiently.
With these proofs in place, decentralized compute can safely run DeFi agents, delegate rollup proofs to thousands of untrusted nodes, and support fully auditable AI inference. Open, permissionless networks of provers could compete based on speed and cost, making dishonesty mathematically impossible. This approach works purely on “just math” without relying on reputation scores or slashing mechanisms.
Simply decentralizing GPUs is not enough. True decentralized compute requires verifiable proofs for every teraflop, ensuring that every output is both unforgeable and fully auditable.
What Does This Mean for the Market?
Without cryptographic verification, the Total Addressable Market for decentralized compute remains confined to rendering tasks and hobbyist AI projects. High-value enterprise applications, such as DeFi bots, medical inference, and proprietary AI models, require provable correctness to ensure reliability and security. The $2 billion to $3 billion invested in decentralized cloud tokens between 2023 and 2025 has mostly gone toward building coordination layers rather than systems capable of verifiable computation.
Only those networks that implement scalable cryptographic proofs will be able to support enterprise adoption, allowing complex and sensitive workloads to run securely and trustlessly on decentralized infrastructure.
Conclusion
Decentralized compute is at an important turning point. Networks that provide unbreakable proofs for every computation could completely change how Web3 operates. When results can be verified mathematically sensitive tasks like DeFi operations, AI inference, and rollups can run safely without depending on trusted nodes.
Glossary
Trustless Computing: Users can verify results without trusting a third party.
Sybil Attack: One actor fakes multiple identities to manipulate a network.
Node Operator: A participant that runs computations and reports results.
Total Addressable Market (TAM): The full potential market size.
Decentralized Cloud Tokens: Tokens to pay and manage decentralized compute.
Frequently Asked Questions Decentralized Compute
Why has decentralized compute failed?
It has failed as users still have to trust node operators. And there is no way to mathematically verify results.
Why can’t Web3 GPU networks be fully trusted?
The results are only backed by reputation scores and not cryptographic proofs.
How do decentralized GPU networks work?
They find available GPUs and coordinate payments across nodes to perform tasks.
What are some real failures in decentralized compute?
Corrupted Blender renders and Sybil attacks have shown that networks can be manipulated.
What is the future of decentralized compute?
It will be safe and trustless when networks use cryptographic proofs to verify every result.