This article was first published on Deythere.
- What Did the BONK.fun hack Reveal About the Platform’s Security Incident?
- How Did BONK.fun Build Its Position in the Solana Launchpad Market?
- Why Did User Activity and Market Share Decline Before the Breach?
- Are Front-End Phishing Attacks Increasing Across Crypto Platforms?
- What Steps Are Being Taken to Protect Users?
- Conclusion
- Glossary
- Frequently Asked Questions About BONK.Fun Hack
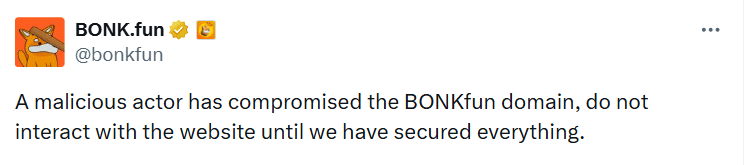
BONK.fun hack raised new concerns across the Solana ecosystem after attackers took control of the launchpad’s domain and placed a wallet-draining script on the website, putting users’ funds at possible risk. The incident unfolded on Thursday when a malicious actor hijacked a team account connected to the platform and pushed a malicious prompt through the site. The project team issued urgent warnings asking users not to interact with the domain until security checks were completed.
The Solana-based launchpad, known for enabling token creation without coding, briefly became a risk point for wallet connections after the compromise. Team members alerted the community through official social channels while security teams began investigating the breach. The incident highlighted how front-end attacks continue to threaten crypto platforms even as blockchain infrastructure expands.
What Did the BONK.fun hack Reveal About the Platform’s Security Incident?
The BONK.fun hack happened after attackers gained control of a team account and used it to place a wallet drainer on the platform’s domain. Once the site was compromised, visitors were shown a fake terms-of-service (TOS) message that looked genuine. Anyone who approved this prompt unknowingly allowed a transaction that could remove funds from their connected crypto wallets.

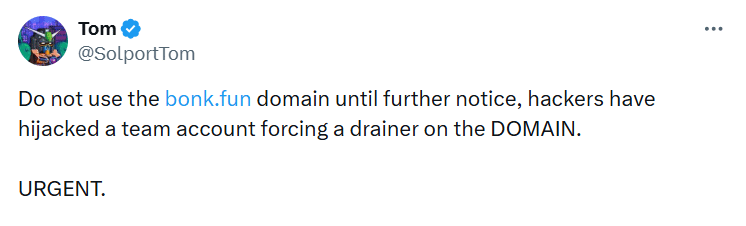
The attack relied on tricking users into signing a wallet request rather than breaking any blockchain security system. The platform’s official account on X warned the community that “a malicious actor has compromised the BONKfun domain” and advised users not to interact with the website until security measures were fully restored. Tom, an operator linked to the project, shared a separate warning on X.
He wrote, Do not use the http://bonk.fun domain until further notice, hackers have hijacked a team account forcing a drainer on the DOMAIN.” The team later explained that the incident only impacted users who signed the fake TOS message after the compromise occurred. Wallets that had previously connected to the platform or tokens traded through external terminals were not affected.
How Did BONK.fun Build Its Position in the Solana Launchpad Market?
Before the BONK.fun hack, the platform had grown quickly within the Solana ecosystem. BONK.fun started in April 2025 with backing from the BONK community and Raydium. The platform allowed users to create and launch tokens without needing coding knowledge through a bonding-based mechanism.
This simple system attracted many creators in a short time. At its peak, the launchpad controlled around 84% of Solana’s launchpad market share, moving far ahead of competing platforms such as Pump.fun. Because of this rapid adoption, BONK.fun became one of the most widely used platforms for launching tokens on the Solana network during 2025.
Why Did User Activity and Market Share Decline Before the Breach?
Interest in the platform started to decline several months before the BONK.fun hack. Many users said that rewards were becoming more difficult to earn and successful token launches were happening less often. By the end of 2025, BONK.fun’s share of the Solana launchpad market had dropped sharply to about 7%. Around the same time, Pump.fun began gaining strength again after focusing on acquisitions and improving its scalability.
The gap between the two platforms was also visible in revenue results. Pump.fun generated around $720,000, while BONK.fun brought in about $84,000. To bring back user activity, BONK.fun removed its platform fees and set them at 0% in early 2026. The decision led to a short increase in participation, but the momentum did not last for long.
Are Front-End Phishing Attacks Increasing Across Crypto Platforms?
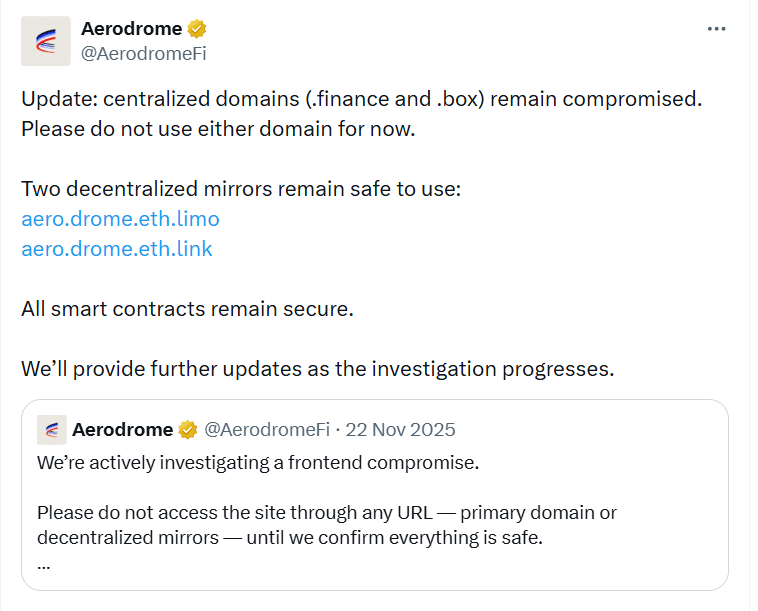
Incidents like the BONK.fun hack show a wider pattern of front-end attacks that are increasingly targeting crypto platforms. A similar case happened in November 2025 when Aerodrome Finance reported a front-end breach connected to its centralized domains. The project warned users to avoid visiting those domains while the issue was being investigated. Another example involved a phishing scam related to MetaMask that was identified by an X user known as SECUR3.
In that incident attackers showed a fake “MetaMask Urgent Update” message together with a false two-factor authentication page. One user reportedly lost $50,000 within just ten seconds after clicking the harmful link. These examples demonstrate that attackers are increasingly using misleading website prompts and wallet approval requests instead of trying to break blockchain protocols directly.
What Steps Are Being Taken to Protect Users?
After the BONK.fun hack the project team asked users to avoid interacting with the platform’s domain until security checks were finished. The breach was still being investigated when the warning was issued. The team did not reveal how many users might have approved the malicious transaction or the possible value of funds that could have been lost. Early alerts shared through social media helped spread the warning quickly across the community.

Security experts usually advise users to check website addresses carefully before connecting their wallets or approving any transaction requests. Tools such as Revoke.cash can help remove risky permissions that may have been granted during suspicious activity. Platforms are also expected to improve DNS protection and website security to reduce the chances of similar incidents happening again.
Conclusion
BONK.fun hack brought new attention to the risks that appear when attackers manage to interfere with the web infrastructure used by crypto platforms. In this case, the compromised domain displayed a harmful prompt to visitors. Anyone who accepted the fake terms-of-service message could unknowingly approve a transaction that allowed funds to be taken from their connected wallet.
The team moved quickly to warn users and started reviewing the incident, but the BONK.fun hack showed how phishing tactics still pose a challenge for decentralized platforms. As the investigation continued, the situation also highlighted the importance of being careful when approving wallet requests and the need for stronger domain and website security across the crypto industry.
Glossary
Wallet Drainer: Tool that steals crypto after a user approves a wallet transaction.
Compromised Domain: A website taken over by attackers to run malicious activity.
Solana Launchpad: Platform on Solana used to create and launch tokens.
DNS Security: Protection that prevents domain hijacking or redirection.
Crypto Front End Security: Safeguards that protect crypto platform websites.
Frequently Asked Questions About BONK.Fun Hack
What is the BONK.fun hack?
It is security incident where attackers took control of platform’s domain and tried to drain funds from users’ wallets.
How did the BONK.fun hack happen?
The hack happened after attackers hijacked team account and placed a malicious wallet drainer on website.
Were all BONK.fun users affected by the hack?
No, only users who signed fake terms of service message on the compromised website were at risk.
Why are phishing attacks common in crypto?
It is comman as attackers try to trick users into approving harmful wallet transactions.
Is BONK.fun investigating hack?
BONK.fun team said they are investigating the incident and working to secure the platform.